Cloud Security for Lawyers: Understanding IAM, Encryption, and Zero Trust Without the Jargon
You're an attorney. You went to law school to argue cases and advise clients, not to become a cybersecurity expert. But here's the reality: the ABA says you have an ethical obligation to understand...

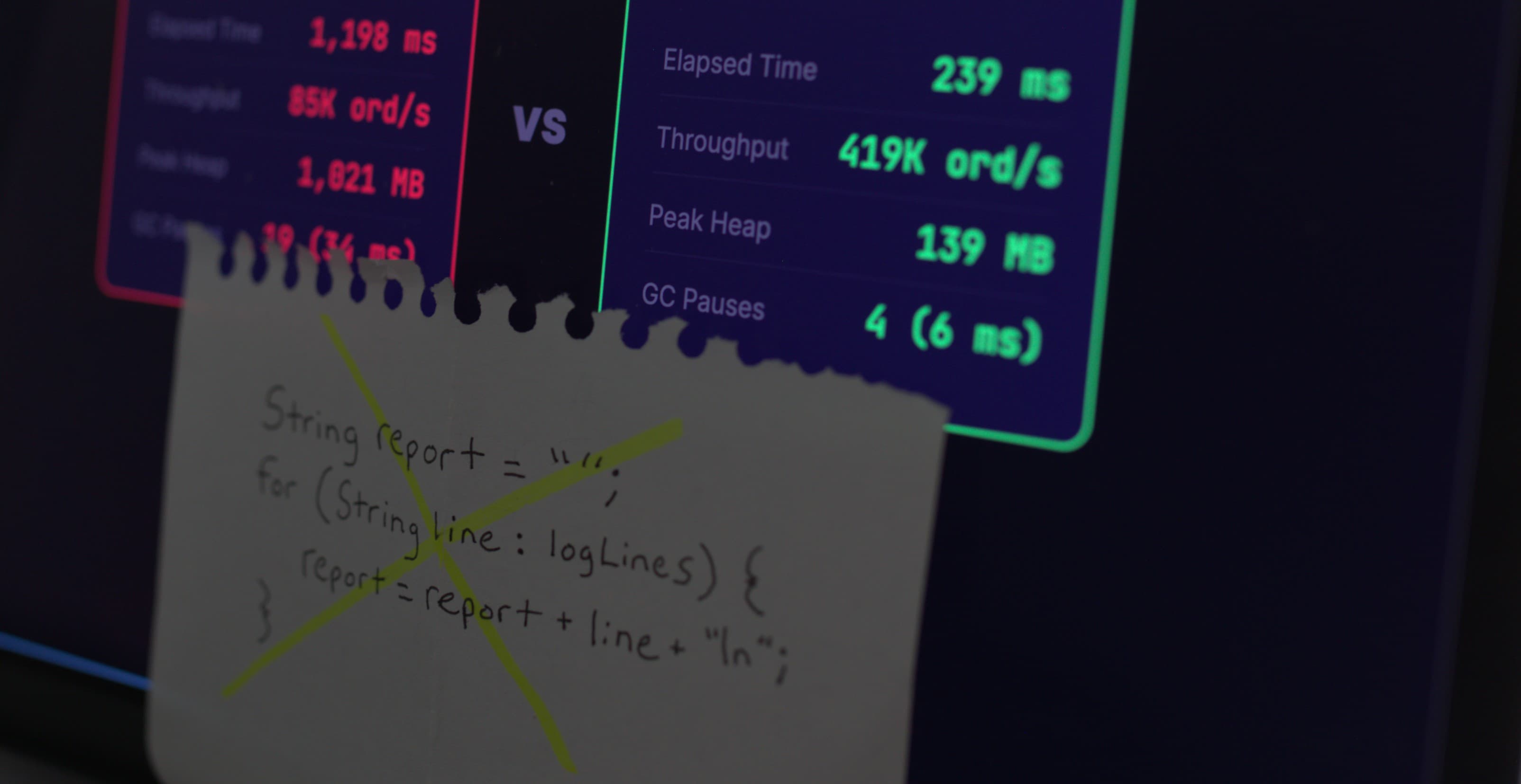
Source: DEV Community
You're an attorney. You went to law school to argue cases and advise clients, not to become a cybersecurity expert. But here's the reality: the ABA says you have an ethical obligation to understand the technology you use to handle client data. Model Rule 1.1 requires you to stay current with "the benefits and risks associated with relevant technology." Model Rule 1.6(c) says you need to make "reasonable efforts" to prevent unauthorized access to client information. That doesn't mean you need to configure firewalls or write security policies from scratch. It means you need to understand the core concepts well enough to ask the right questions, evaluate your vendors, and make informed decisions about how your firm handles sensitive data. We're going to cover three big ideas in cloud security: Identity and Access Management (IAM), encryption, and Zero Trust. By the end, you'll know what each one means in plain language, why it matters for your practice, and what questions to ask your IT t